How to Find Email Addresses for Business Growth in 2026
March 21, 2026
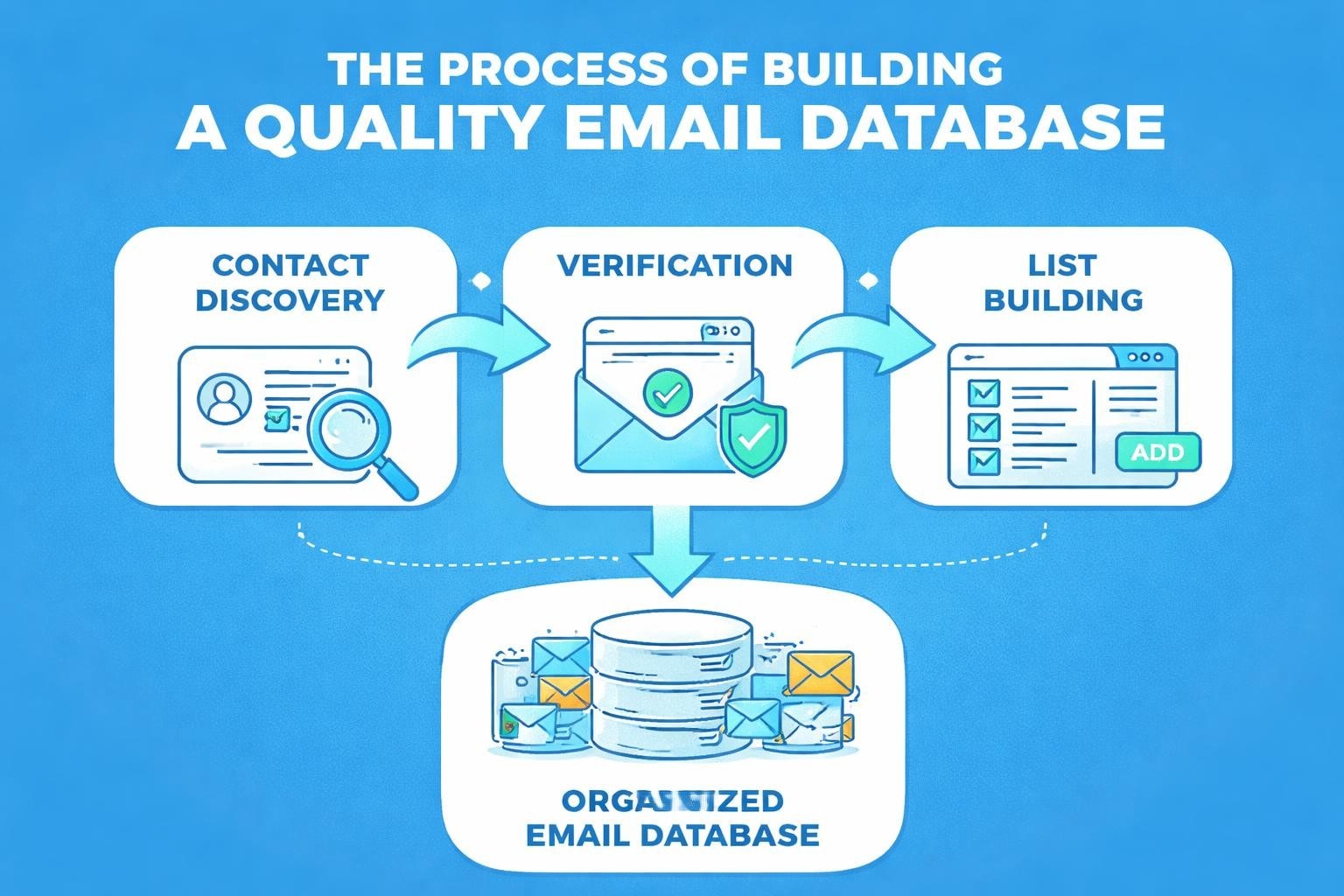
Building a robust email marketing database requires knowing how to find email addresses ethically and efficiently. For small businesses competing in 2026's digital landscape, the ability to locate and verify contact information represents a fundamental skill that drives customer acquisition, partnership development, and market expansion. Whether you're reaching out to potential clients, connecting with industry influencers, or building relationships with suppliers, finding accurate email addresses forms the foundation of successful business communication.
Understanding the Importance of Quality Email Discovery
When you find email addresses for your business, quality always trumps quantity. A database filled with verified, permission-based contacts delivers significantly better results than a massive list of unverified or purchased addresses. Small businesses especially benefit from this targeted approach, as it maximises return on investment whilst maintaining compliance with data protection regulations.
The value of authentic contact discovery includes:
- Higher engagement rates from genuinely interested recipients
- Improved sender reputation and deliverability scores
- Reduced bounce rates and spam complaints
- Better compliance with GDPR and other privacy regulations
- Enhanced brand reputation through ethical practices
Modern email marketing success depends on building relationships with real people who have expressed genuine interest in your products or services. This philosophy aligns perfectly with building a clean and engaged email database, which emphasises permission-based collection methods.
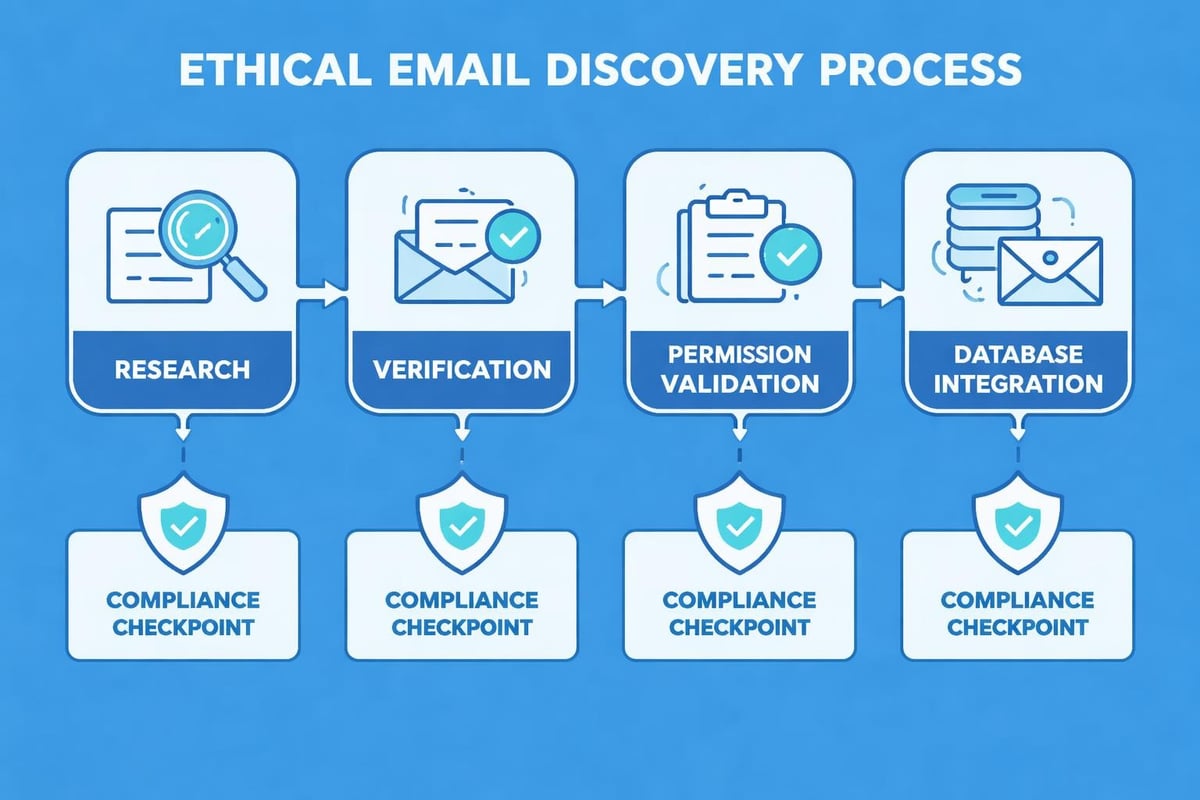
The Ethical Framework
Before exploring methods to find email information, establishing ethical boundaries proves essential. Respect for privacy, adherence to regulations, and commitment to transparent communication practices protect both your business reputation and recipient trust.
Professional Methods to Locate Contact Information
Finding business email addresses requires a systematic approach that combines multiple techniques. Each method offers distinct advantages depending on your specific needs and target audience.
Company Website Investigation
Most organisations display contact information directly on their websites, making this your first research destination. Navigate to "About Us," "Contact," or "Team" pages where businesses typically publish email addresses for customer communication.
Key areas to examine:
- Contact forms that may reveal email formatting patterns
- Footer sections containing general enquiry addresses
- Staff directories with individual team member contacts
- Press or media pages designed for journalist outreach
- Customer service sections with support email addresses
When examining company websites, pay attention to email address patterns. If you discover that [email protected] works in sales, you can reasonably infer that [email protected] might follow the same format.
Social Media Platform Research
Professional networking platforms provide valuable resources to find email addresses, particularly for B2B communications. LinkedIn profiles often include contact information, whilst company pages may list official communication channels.
You can find someone's email on Facebook by checking their 'About' section or examining publicly shared posts where people sometimes include contact details. However, respect privacy settings and platform terms of service when conducting this research.
| Platform | Best For | Success Rate |
|---|---|---|
| Professional contacts | High | |
| Local businesses | Medium | |
| Twitter/X | Industry influencers | Medium |
| Creative professionals | Low-Medium |
Email Discovery Tools and Databases
Specialised software tools can accelerate your search when you need to find email addresses at scale. These platforms use various techniques including web scraping, database aggregation, and pattern recognition to locate contact information.
Popular categories include:
- Email finder tools that search public databases and websites
- Verification services that confirm address validity
- Chrome extensions that extract emails whilst browsing
- Domain search tools that discover all emails associated with a company
Always verify discovered addresses before adding them to your marketing lists. Invalid or outdated contacts damage sender reputation and waste resources.
Building Your Database Ethically and Legally
Once you find email addresses, proper handling ensures compliance and effectiveness. Understanding email address harvesting helps you avoid practices that harm your reputation or violate regulations.
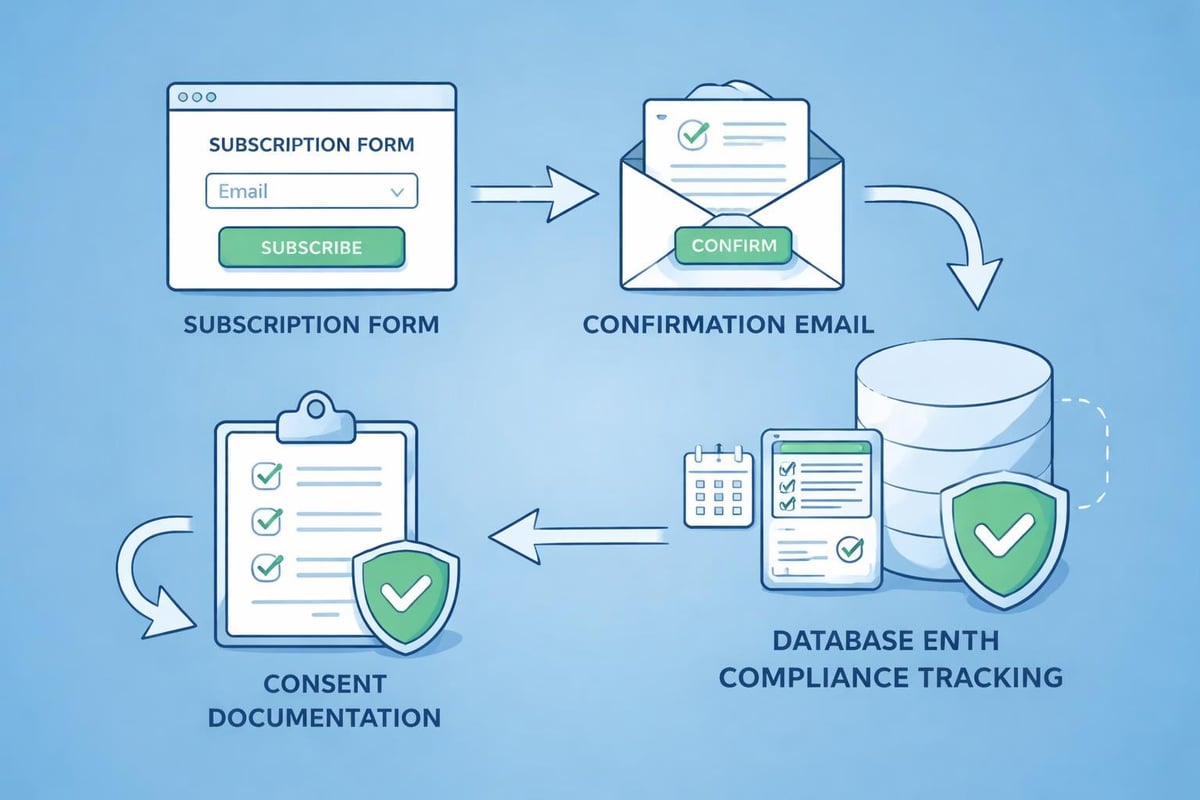
Permission and Consent Requirements
The most critical aspect of email list building involves obtaining proper permission. Even when you successfully find email contacts, sending unsolicited commercial messages without consent violates regulations in most jurisdictions.
Double opt-in processes provide optimal protection:
- Recipient submits email address through your form
- System sends confirmation email requiring action
- Recipient clicks confirmation link
- System adds verified address to your database
- Welcome email confirms subscription
This approach ensures that every subscriber genuinely wants to receive your communications, aligning with the principles outlined in Astonish Email's antispam policy.
Data Protection Compliance
GDPR, PECR, and similar regulations govern how businesses collect, store, and use email addresses. When you find email information through any method, you must handle it according to strict legal requirements.
Keep detailed records of:
- How and when you obtained each address
- What consent the individual provided
- Which communications they agreed to receive
- When they subscribed or opted out
- How you secure their personal data
Understanding professional email address management helps maintain compliance whilst building effective marketing campaigns.
Advanced Strategies for Contact Discovery
Beyond basic methods, sophisticated approaches help you find email addresses for specific business needs. These techniques require more effort but deliver higher-quality results for targeted outreach.
Content-Driven Collection
Creating valuable content that requires email registration generates qualified leads naturally. Whitepapers, industry reports, webinars, and exclusive tools encourage prospects to share contact information willingly.
This strategy works because:
- Recipients self-identify their interests
- You demonstrate expertise before first contact
- The exchange feels fair and valuable
- Permission is explicit and documented
- Subscribers expect relevant follow-up
When implementing this approach through your email marketing platform, ensure your content genuinely delivers promised value.
Event and Trade Show Collection
In-person and virtual events provide excellent opportunities to find email addresses from highly relevant contacts. Attendees at industry conferences, trade shows, or webinars have already demonstrated interest in your sector.
| Collection Method | Engagement Level | Follow-up Window |
|---|---|---|
| Business cards | Medium | 48-72 hours |
| Badge scanning | Low-Medium | 24-48 hours |
| Registration forms | High | Immediate |
| Competition entries | Medium-High | 24 hours |
Always inform event attendees how you'll use their information and provide clear opt-in mechanisms for ongoing communications.
Partnership and Co-marketing
Collaborating with complementary businesses allows you to find email contacts within new but relevant audiences. Co-hosted webinars, shared content, or joint promotions introduce your brand to pre-qualified prospects.
Establish clear agreements about:
- How collected addresses will be shared
- What permissions cover both businesses
- Which communications each party can send
- How opt-outs will be honoured across both lists
- Data security and privacy responsibilities
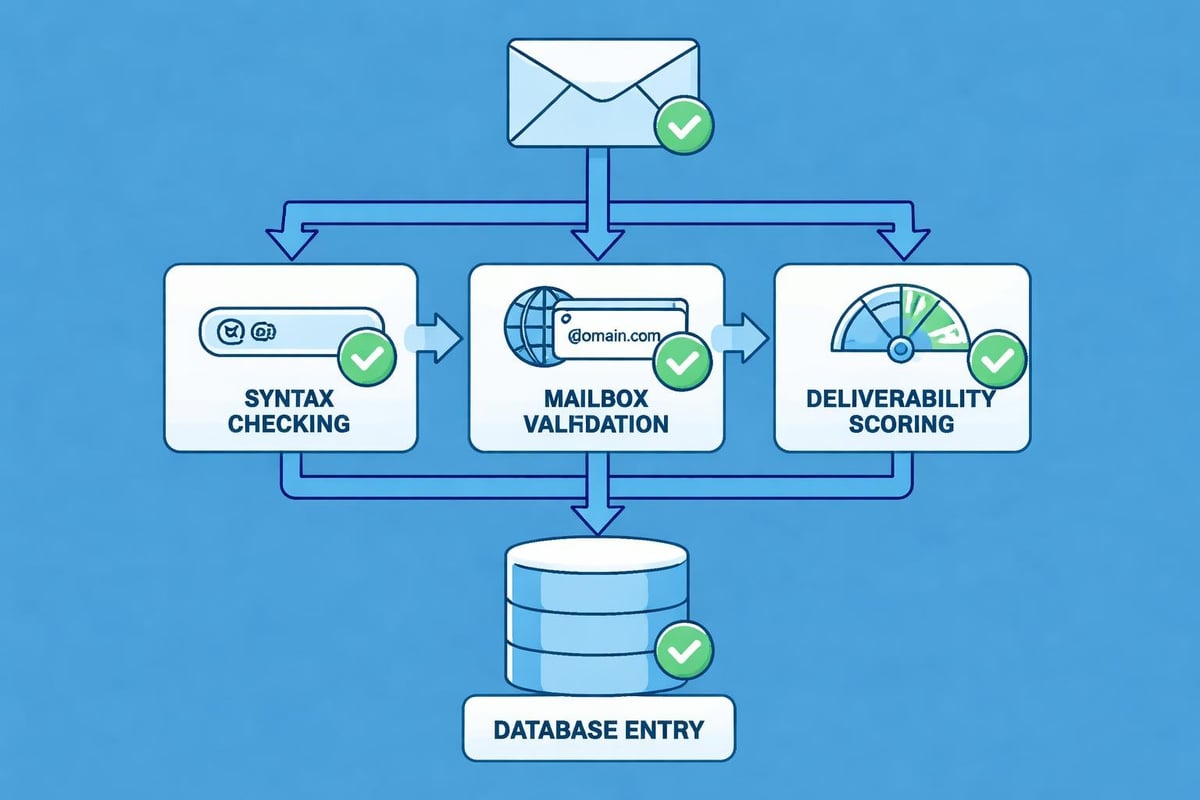
Verification and List Hygiene Practices
After you find email addresses, maintaining list quality requires ongoing attention. Regular verification prevents common problems that damage deliverability and campaign performance.
Real-time Verification
Validate email addresses at the point of collection to prevent typos, fake addresses, and temporary emails from entering your database. Real-time verification checks syntax, domain validity, and mailbox existence before accepting submissions.
Verification catches common issues:
- Typographical errors (gmial.com instead of gmail.com)
- Disposable email services used to avoid engagement
- Role-based addresses that may violate platform policies
- Duplicate submissions from the same contact
- Obvious spam or bot-generated addresses
Implementing these checks when you send out emails protects your sender reputation from the start.
Regular Database Maintenance
Email lists naturally decay as people change jobs, abandon addresses, or lose interest. Plan quarterly reviews to remove inactive subscribers and update outdated information.
- Identify inactive subscribers who haven't engaged in 6-12 months
- Send re-engagement campaigns offering one final opportunity
- Remove non-responders to maintain list health
- Suppress hard bounces immediately
- Monitor engagement trends across segments
This maintenance aligns with email security best practices that protect both your business and subscribers.
Segmentation After Discovery
Once you find email addresses and build your list, strategic segmentation dramatically improves campaign performance. Grouping contacts by shared characteristics enables personalised messaging that resonates with specific audience segments.
Segmentation Criteria
Different businesses require different segmentation approaches based on their products, services, and customer journeys. Consider these common dimensions:
Demographic segmentation:
- Company size and revenue
- Industry or sector
- Geographic location
- Job title or department
Behavioural segmentation:
- Purchase history and frequency
- Website interaction patterns
- Email engagement levels
- Product preferences
Lifecycle segmentation:
- New subscribers
- Active customers
- Lapsed buyers
- Brand advocates
Effective segmentation transforms a generic email list into a powerful marketing asset. When you understand business email for small business contexts, you can craft messages that address specific pain points and opportunities.
Dynamic Segmentation
Modern email marketing platforms enable dynamic segments that automatically update based on subscriber behaviour. These living lists ensure your messaging remains relevant as contacts move through different stages of the customer journey.
Set up automated segments that trigger when subscribers:
- Make their first purchase
- Reach engagement milestones
- Show signs of declining interest
- Demonstrate high purchase intent
- Complete specific actions on your website
Security Considerations When Handling Email Data
Protecting the email addresses you collect represents both a legal obligation and a trust responsibility. Security breaches damage your reputation, trigger regulatory penalties, and undermine subscriber confidence.
Storage and Access Controls
Implement robust security measures for databases containing email addresses and associated personal information. Encryption, access restrictions, and regular security audits prevent unauthorised access.
Following email security best practices for IT teams helps establish comprehensive protection protocols that safeguard subscriber data throughout its lifecycle.
Essential security measures include:
- Encrypted database storage
- Role-based access permissions
- Two-factor authentication for system access
- Regular security audits and penetration testing
- Incident response procedures
Avoiding Phishing and Fraud Risks
When communicating with contacts you've worked to find email addresses for, protect them from phishing attempts and fraud. Authentic, trustworthy communication patterns help subscribers recognise legitimate messages from your business.
Research on URL inspection tasks for phishing detection demonstrates the importance of training both your team and your subscribers to recognise suspicious emails. Clear branding, consistent sender addresses, and transparent communication build trust that protects everyone.
Maximising ROI from Your Contact Database
Finding quality email addresses represents just the beginning. Converting those contacts into engaged subscribers and paying customers requires strategic nurturing and value delivery.
Welcome Series Design
First impressions significantly influence long-term engagement. When someone joins your list, a well-crafted welcome series sets expectations, delivers immediate value, and begins building the relationship.
| Email # | Timing | Purpose | Key Element |
|---|---|---|---|
| 1 | Immediate | Confirm subscription | Quick win/value |
| 2 | 2-3 days | Introduce brand story | Personal connection |
| 3 | 5-7 days | Showcase key offerings | Clear next steps |
| 4 | 10-14 days | Social proof/testimonials | Trust building |
This systematic approach transforms contacts you find email addresses for into engaged community members who anticipate and value your communications.
Ongoing Value Delivery
Maintain engagement through consistent value delivery that addresses subscriber needs and interests. Educational content, exclusive offers, and helpful resources justify the inbox space your messages occupy.
Balance promotional content with genuinely useful information:
- 80% educational/valuable content that helps subscribers succeed
- 20% promotional content that presents relevant offers
Understanding email benefits helps you articulate why subscribers should maintain their connection with your brand.
Measuring Success and Optimising Performance
Track key metrics to evaluate the quality of email addresses you find and the effectiveness of your campaigns. Data-driven decisions improve results whilst identifying areas requiring adjustment.
Essential Performance Metrics
Monitor these indicators to gauge list health and campaign effectiveness:
Deliverability metrics:
- Bounce rate (hard and soft)
- Spam complaint rate
- Inbox placement rate
Engagement metrics:
- Open rate
- Click-through rate
- Conversion rate
- List growth rate
- Unsubscribe rate
Set benchmarks based on industry standards and your historical performance, then work systematically to improve each metric over time.
A/B Testing for Continuous Improvement
Experiment with different approaches to discover what resonates with the contacts you've worked to find email addresses for. Test subject lines, send times, content formats, and calls-to-action to optimise performance.
Effective testing framework:
- Identify one variable to test
- Create two variations (A and B)
- Split your list randomly
- Send to statistically significant sample
- Analyse results and implement winner
- Document learnings for future campaigns
This systematic improvement process ensures your email marketing delivers increasing returns as you refine your approach based on real subscriber behaviour.
Successfully building an email marketing database requires combining ethical discovery methods with rigorous verification and strategic segmentation. By focusing on permission-based collection and delivering consistent value, small businesses can develop powerful marketing assets that drive sustainable growth. When you're ready to transform your contact list into revenue-generating campaigns, Astonish Email provides the tools and support small businesses need to execute professional email marketing strategies that deliver measurable results.