Email System: A Complete Guide for Small Business Success
March 18, 2026
An email system forms the backbone of modern business communication, enabling companies to connect with customers, collaborate internally, and build lasting relationships. For small businesses in 2026, understanding how these systems work and how to optimise them isn't just technical knowledge-it's essential for growth, security, and professional credibility. Whether you're setting up your first business email system or improving your current infrastructure, knowing the fundamentals will help you make informed decisions that protect your data and enhance customer engagement.
Understanding Email System Architecture
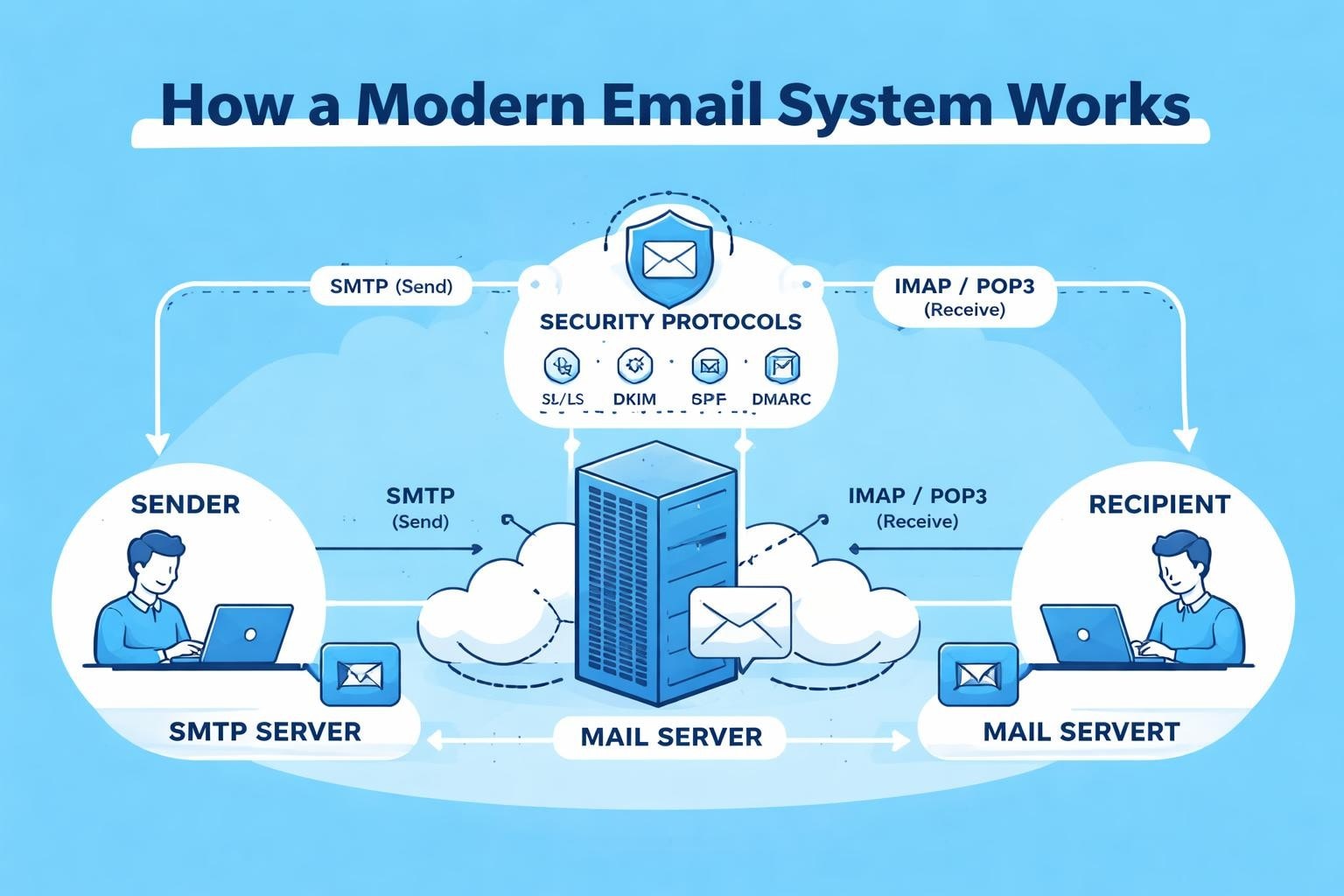
A modern email system comprises multiple interconnected components working together to ensure messages reach their destinations securely and reliably. At its core, the system includes mail servers, protocols, authentication mechanisms, and client applications that facilitate the entire communication process.
Core Components and Their Functions
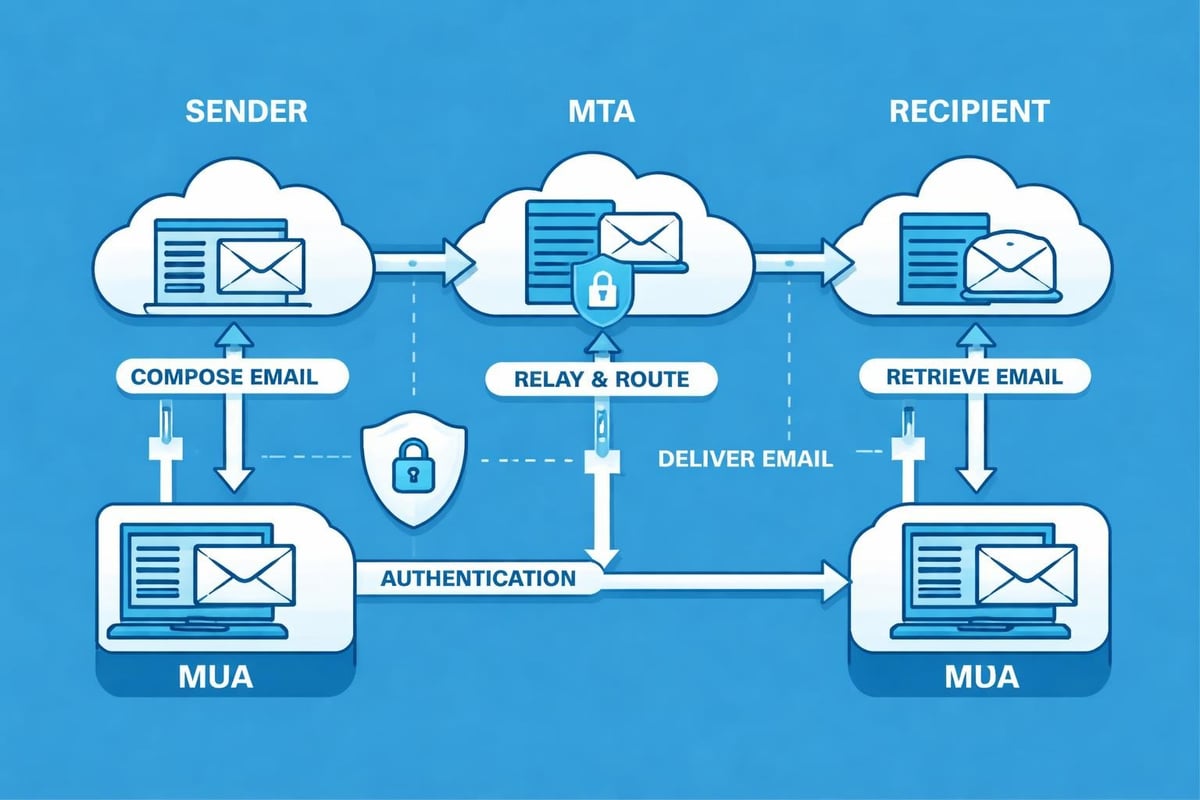
Mail Transfer Agents (MTAs) handle the routing and delivery of messages between servers, whilst Mail Delivery Agents (MDAs) manage the final delivery to recipient mailboxes. Mail User Agents (MUAs) are the applications users interact with-whether web-based or desktop clients-to compose, send, and read messages.
The relationship between these components ensures seamless operation:
- MTAs use SMTP (Simple Mail Transfer Protocol) to transfer messages between servers
- MDAs place incoming messages into the appropriate mailboxes
- MUAs retrieve messages using IMAP or POP3 protocols
- Authentication servers verify sender and recipient identities
Understanding this architecture helps small businesses select the right infrastructure for their needs. When choosing email marketing platforms, knowing these fundamentals ensures compatibility and scalability.
Protocol Standards That Power Email Communication
Multiple protocols work in harmony to make email systems functional. SMTP remains the standard for sending messages, whilst IMAP (Internet Message Access Protocol) and POP3 (Post Office Protocol version 3) handle retrieval. IMAP offers superior functionality for modern businesses, allowing multiple devices to synchronise mailbox contents and maintain message states across platforms.
| Protocol | Primary Function | Business Advantage |
|---|---|---|
| SMTP | Message transmission | Universal compatibility |
| IMAP | Message retrieval and synchronisation | Multi-device access |
| POP3 | Message download | Offline access |
| HTTPS | Secure web access | Protected credentials |
These protocols form the foundation upon which reliable email systems operate, ensuring messages flow smoothly regardless of sender or recipient infrastructure.
Security Essentials for Business Email Systems
Security represents perhaps the most critical aspect of any email system in 2026. With cyber threats evolving constantly, small businesses must implement robust protection measures to safeguard sensitive communications and maintain customer trust.
Authentication Protocols and Verification
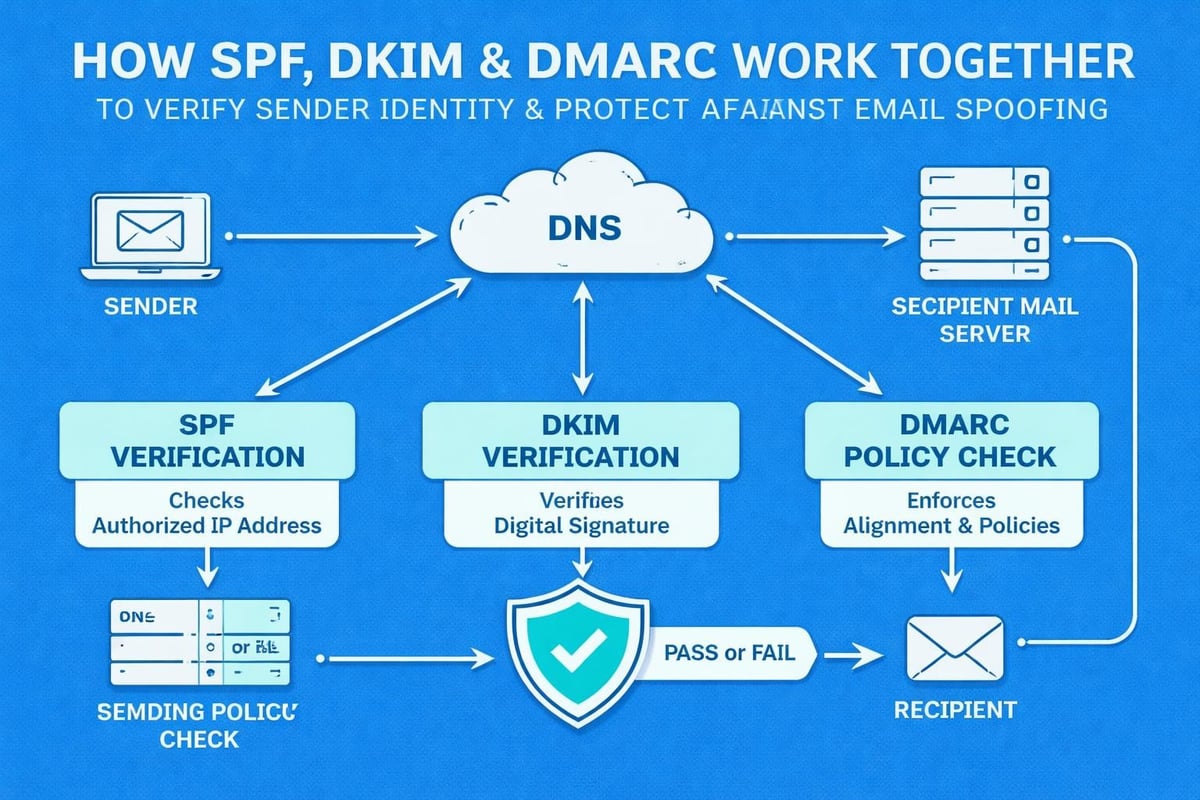
Modern email systems rely on three primary authentication methods to prevent spoofing and phishing. SPF (Sender Policy Framework) allows domain owners to specify which mail servers can send messages on their behalf, as detailed in IBM's comprehensive email security overview. The Sender Policy Framework works by publishing DNS records that receiving servers can verify before accepting messages.
DKIM (DomainKeys Identified Mail) adds digital signatures to outgoing messages, enabling recipients to verify that content hasn't been altered during transmission. DMARC (Domain-based Message Authentication, Reporting, and Conformance) builds upon SPF and DKIM, providing domain owners with policy enforcement and reporting capabilities.
Implementing these three protocols should be non-negotiable for any business email system. They work together to:
- Verify sender identity
- Detect message tampering
- Prevent domain impersonation
- Provide visibility into authentication failures
- Protect brand reputation
Encryption and Data Protection
Encryption protects email content both in transit and at rest. Transport Layer Security (TLS) encrypts connections between mail servers, preventing interception during transmission. For sensitive communications, modern encryption protocols like PGP (Pretty Good Privacy) and S/MIME (Secure/Multipurpose Internet Mail Extensions) provide end-to-end protection.
Multi-factor authentication (MFA) adds another security layer by requiring additional verification beyond passwords. This simple measure dramatically reduces unauthorised access risks, even when credentials become compromised.
Businesses should follow established email security best practices to protect their email systems comprehensively. These include regular security audits, employee training on phishing recognition, and implementing secure email gateways that filter malicious content before it reaches user inboxes.
Optimising Email System Performance
Performance optimisation ensures your email system delivers messages promptly whilst maintaining high deliverability rates. For small businesses engaged in email marketing campaigns, optimisation directly impacts campaign success and customer engagement.
Deliverability Factors and Reputation Management
Email deliverability-the percentage of messages reaching recipient inboxes rather than spam folders-depends on multiple factors. Sender reputation ranks amongst the most influential, with ISPs tracking sending patterns, complaint rates, and engagement metrics to determine trustworthiness.
Building and maintaining strong sender reputation requires:
- Consistent sending patterns without sudden volume spikes
- Low bounce rates through regular list hygiene
- Minimal spam complaints
- Strong engagement rates (opens, clicks)
- Proper authentication implementation
IP warming proves essential when launching a new email system or adding dedicated IP addresses. This gradual volume increase demonstrates legitimate sending patterns to ISPs, establishing trust before ramping up to full capacity.
Technical Configuration for Maximum Reliability
Proper DNS configuration underpins email system reliability. Beyond authentication records, businesses must configure:
| Record Type | Purpose | Configuration Priority |
|---|---|---|
| MX Records | Mail server routing | Critical |
| SPF Records | Sender authorisation | Critical |
| DKIM Records | Message signing | Critical |
| DMARC Records | Policy enforcement | High |
| PTR Records | Reverse DNS lookup | High |
Message formatting impacts deliverability significantly. Clean HTML code, appropriate text-to-image ratios, and mobile-responsive designs ensure messages render correctly across various email clients whilst avoiding spam triggers.
List segmentation and targeted sending improve both engagement and system efficiency. Rather than sending identical messages to entire databases, segmentation allows personalised content delivery to specific audience segments, improving relevance and reducing resource consumption.
Email System Selection and Implementation
Choosing the right email system involves evaluating business requirements, budget constraints, and technical capabilities. Small businesses face a fundamental decision between self-hosted solutions and cloud-based services.
Hosted Versus Cloud-Based Solutions
Self-hosted email systems offer complete control over infrastructure, data, and configuration. However, they require significant technical expertise, ongoing maintenance, and security management. Server hardware, software licences, backup systems, and dedicated IT staff create substantial overhead.
Cloud-based email systems eliminate infrastructure management whilst providing enterprise-grade features at accessible price points. These platforms handle:
- Server maintenance and updates
- Security patches and monitoring
- Backup and disaster recovery
- Scalability and resource allocation
- Compliance and data protection
For most small businesses, cloud-based solutions provide superior value. The reduced complexity allows teams to focus on communication strategy rather than technical administration. When exploring available plans, consider features that align with specific business needs rather than simply comparing price points.
Essential Features for Small Business Email Systems
Modern business email systems should include capabilities beyond basic message delivery. Integration with customer relationship management (CRM) tools, marketing automation platforms, and analytics systems creates a cohesive communication ecosystem.
Key features to prioritise include:
- Automation capabilities for triggered messages and workflows
- Segmentation tools for targeted communication
- Template builders for consistent branding
- Analytics dashboards for performance tracking
- List management and hygiene tools
- Mobile accessibility for on-the-go management
Contact management functionality proves particularly valuable, enabling businesses to maintain detailed subscriber profiles, track engagement history, and personalise communications based on behaviour and preferences.
Managing Email System Compliance and Policies
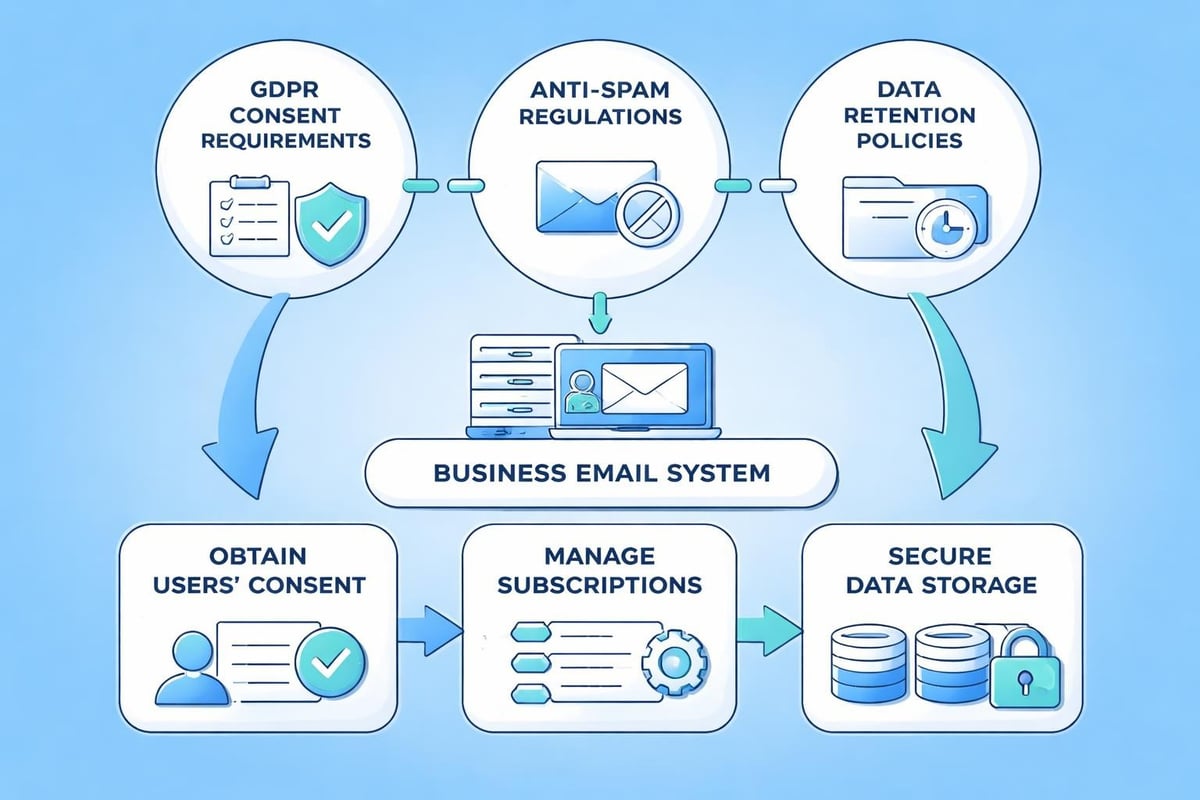
Regulatory compliance isn't optional-it's mandatory for businesses operating email systems in 2026. Multiple regulations govern commercial email communication, with severe penalties for violations.
GDPR and Data Protection Requirements
The General Data Protection Regulation (GDPR) establishes strict requirements for processing personal data, including email addresses. Businesses must obtain explicit consent before adding contacts to mailing lists, provide clear privacy notices, and honour data subject rights including access, rectification, and erasure requests.
Consent management requires documented proof of opt-in, typically through double opt-in processes that verify subscriber intent. This additional step improves list quality whilst ensuring compliance.
Data retention policies determine how long businesses store email data and subscriber information. Clear data retention policies should specify retention periods, deletion procedures, and legal justifications for data processing.
Anti-Spam Regulations and Best Practices
CAN-SPAM (United States), CASL (Canada), and PECR (United Kingdom) regulate commercial email communication with requirements for:
- Accurate header information identifying the sender
- Clear subject lines reflecting message content
- Sender's physical postal address
- Visible and functional unsubscribe mechanisms
- Prompt processing of opt-out requests
Maintaining an antispam policy demonstrates commitment to responsible email practices whilst protecting business reputation. The policy should outline sending practices, consent requirements, and complaint handling procedures.
Advanced Email System Capabilities
Beyond basic functionality, advanced email system features enable sophisticated marketing strategies and deeper customer insights. Small businesses leveraging these capabilities gain competitive advantages through personalisation and automation.
Automation and Workflow Integration
Automated email workflows respond to subscriber actions and behaviours, delivering timely, relevant messages without manual intervention. Welcome series greet new subscribers, abandoned cart sequences recover lost sales, and re-engagement campaigns reconnect with inactive contacts.
Trigger-based automation activates based on specific conditions:
- Subscriber actions (purchases, downloads, form submissions)
- Time-based triggers (anniversaries, renewal dates)
- Behavioural patterns (browsing history, engagement levels)
- Lifecycle stages (new customer, loyal advocate)
Integration capabilities connect email systems with other business tools, creating seamless data flow between platforms. CRM integration ensures sales teams access email engagement data, whilst e-commerce platforms trigger automated order confirmations and shipping notifications.
Analytics and Performance Measurement
Comprehensive analytics transform email systems from communication tools into business intelligence platforms. Beyond basic open and click rates, advanced metrics provide actionable insights into subscriber behaviour and campaign effectiveness.
| Metric Category | Key Indicators | Business Value |
|---|---|---|
| Engagement | Opens, clicks, time spent | Content effectiveness |
| Conversion | Purchases, sign-ups, downloads | Revenue attribution |
| List Health | Growth rate, churn, engagement decay | Audience quality |
| Deliverability | Inbox placement, bounce rates | Technical performance |
A/B testing capabilities enable data-driven optimisation by comparing different message elements. Subject line tests, content variations, and send time experiments identify what resonates with specific audiences, improving results through continuous refinement.
Subscriber journey mapping visualises how contacts interact with email campaigns over time, revealing engagement patterns and identifying opportunities for improved communication strategies. Understanding these journeys helps businesses deliver more relevant content at optimal times.
Email System Maintenance and Optimisation
Ongoing maintenance ensures email systems continue performing optimally whilst adapting to evolving business needs and technological developments. Regular attention to system health prevents issues before they impact deliverability or user experience.
List Hygiene and Database Management
Email lists naturally degrade over time as contacts change addresses, lose interest, or become inactive. Regular list cleaning maintains high engagement rates and protects sender reputation by removing problematic addresses.
List hygiene practices include:
- Removing hard bounces immediately
- Monitoring soft bounces and removing persistent failures
- Identifying and removing spam traps
- Suppressing unengaged subscribers after defined periods
- Validating email syntax and domain validity
Re-engagement campaigns offer one final attempt to reconnect with inactive subscribers before removal. These targeted messages acknowledge the lack of recent engagement and provide easy opt-out options for those no longer interested.
Database segmentation becomes more sophisticated as businesses collect additional subscriber data. Behavioural segmentation based on purchase history, engagement patterns, and content preferences enables increasingly personalised communication that drives better results.
Performance Monitoring and Improvement
Continuous monitoring identifies trends, anomalies, and opportunities for enhancement. Establishing baseline metrics for key performance indicators allows businesses to quickly detect deviations requiring investigation.
Regular review schedules should include:
- Weekly deliverability monitoring
- Monthly engagement trend analysis
- Quarterly strategy assessments
- Annual comprehensive audits
Benchmarking against industry standards provides context for performance evaluation. Whilst every business and audience differs, understanding how metrics compare with similar organisations helps identify strengths and weaknesses.
Security monitoring remains perpetually important, with regular reviews of email security practices ensuring protection against emerging threats. This includes updating authentication protocols, reviewing access permissions, and conducting security awareness training for team members.
Future-Proofing Your Email System
Email technology continues evolving, with artificial intelligence, machine learning, and enhanced privacy measures shaping the future landscape. Businesses building email systems in 2026 should consider emerging trends and prepare for continued evolution.
Emerging Technologies and Capabilities
Artificial intelligence transforms email marketing through predictive send-time optimisation, content personalisation, and automated subject line generation. Machine learning algorithms analyse engagement patterns to determine optimal sending times for individual subscribers, maximising open rates through precise timing.
AI-powered capabilities expanding in 2026 include:
- Predictive analytics forecasting subscriber behaviour
- Dynamic content generation adapting messages to recipients
- Automated image and design optimisation
- Natural language processing improving message clarity
- Sentiment analysis guiding tone and approach
Privacy-enhancing technologies respond to growing consumer demands for data protection. Whilst email security and privacy concerns drive innovation, businesses must balance privacy protection with personalisation capabilities that customers expect.
Scalability and Growth Planning
Email systems must accommodate business growth without requiring complete rebuilds. Selecting platforms with scalable architecture ensures smooth expansion as subscriber lists grow and sending volumes increase.
Scalability considerations include:
- Pricing models that grow with usage rather than creating sudden cost jumps
- API capabilities supporting custom integrations
- Automation sophistication enabling complex workflows
- Team collaboration features supporting multiple users
- Enterprise features available as businesses mature
Platform flexibility allows businesses to start with essential features and add capabilities as needs evolve. This approach controls initial costs whilst ensuring growth pathways remain available when circumstances warrant additional functionality.
Building and maintaining an effective email system requires attention to architecture, security, performance, and compliance whilst leveraging advanced capabilities that drive business results. The right approach combines technical excellence with strategic thinking, creating communication infrastructure that supports current needs and future growth. Astonish Email provides small businesses with the tools, features, and support needed to build professional email marketing systems that deliver results without overwhelming complexity. Discover how our platform can transform your email communication strategy and drive business growth in 2026.